Ever tried logging into an app and been told you’re “not authorized”? That’s where authorization or authorisation comes into play. It might look like a simple spelling difference, but the concept behind it is a crucial part of digital security, legal systems, and everyday access control.
In simple terms, authorization or authorisation refers to the process of granting permission to someone to access resources, data, or services. Whether you’re using American or British English, the meaning stays the same—but the usage, context, and technical importance go much deeper.
Let’s break it down in a clear, practical way so you understand not just what it means, but why it matters.
What Is Authorization or Authorisation?
Authorization US spelling or authorisation (UK spelling) is the process of deciding what an authenticated user is allowed to do.
In other words:
- Authentication = Who are you?
- Authorization = What are you allowed to do?
For example:
- A student logs into a school portal (authentication)
- The system allows them to view grades but not change them (authorization)
Simple Definition:
Authorization or authorisation is the mechanism that controls access rights and permissions after identity is verified.
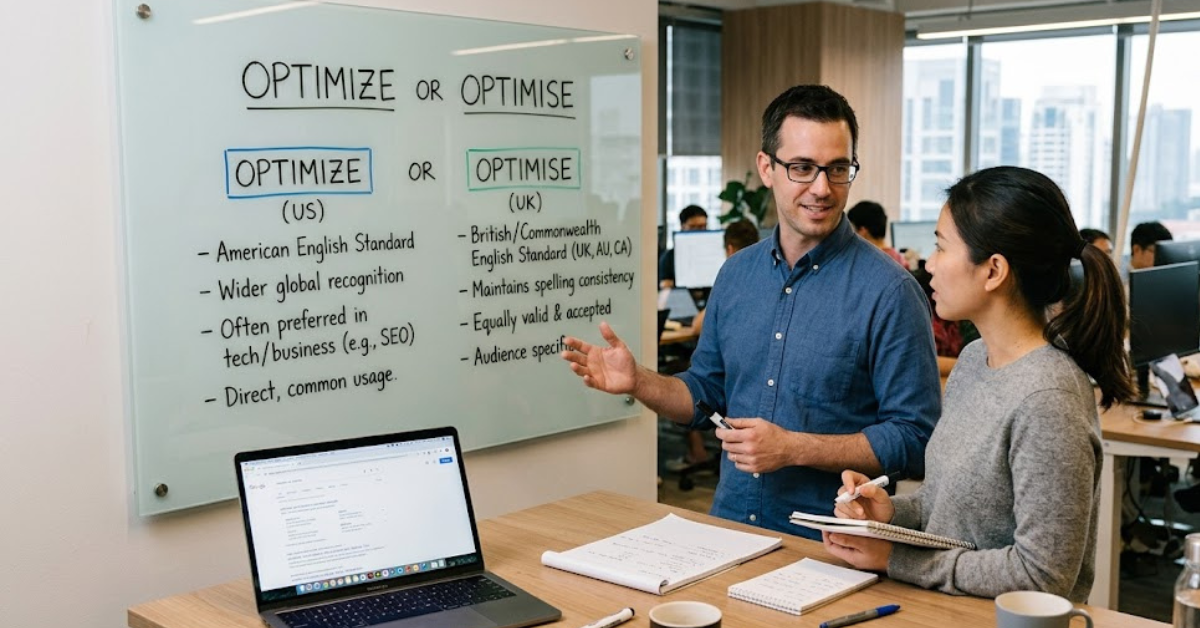
Authorization vs Authorisation: Is There a Difference?
The short answer: No difference in meaning.
The only variation is spelling:
- Authorization → American English
- Authorisation → British English, Australian English, etc.
Both terms are used in:
- Cybersecurity
- Software development
- Law and governance
- Business systems
So whether you see “authorization or authorisation,” the concept remains identical.
Why Authorization or Authorisation Matters in Security
Modern systems rely heavily on authorization or authorisation to protect sensitive data and prevent unauthorized access.
Key reasons it is important:
- Data protection: Ensures only approved users can access confidential information
- Role management: Assigns permissions based on job roles
- System security: Prevents misuse of admin-level controls
- Compliance: Helps meet legal and regulatory requirements
Without proper authorization systems, even strong passwords wouldn’t protect digital platforms.
How Authorization or Authorisation Works in Real Systems
Most modern applications follow a structured process:
1. User Authentication
The system verifies identity (login credentials, biometrics, OTP, etc.).
2. Permission Check
The system checks what the user is allowed to access.
3. Access Decision
Based on rules, access is granted or denied.
Common Models Used:
- Role-Based Access Control (RBAC)
- Attribute-Based Access Control (ABAC)
- Policy-Based Access Control (PBAC)
Authorization or Authorisation in Cybersecurity
In cybersecurity, authorization or authorisation is a core layer of defense.
It ensures:
- Employees only access relevant company data
- Hackers cannot escalate privileges easily
- Systems maintain controlled environments
Example:
In a banking app:
- Customers can view balances
- Managers can approve transactions
- Admins can modify system settings
Each level is defined by authorization rules.
Common LSI Keywords Related to Authorization or Authorisation
To better understand the topic, here are related terms often used:
- Access control
- User permissions
- Identity management
- Security policies
- Authentication and authorization
- Digital security systems
- Privilege management
Best Practices for Strong Authorization Systems
Organizations follow certain practices to keep systems secure:
- Apply least privilege principle (give minimum required access)
- Regularly update user roles
- Use multi-layer security controls
- Monitor access logs
- Separate admin and user permissions
These steps reduce the risk of unauthorized actions and data breaches.
FAQs About Authorization or Authorisation
1. What is authorization or authorisation in simple terms?
It is the process of giving someone permission to access specific resources or perform certain actions after verifying their identity.
2. Is authorization the same as authentication?
No. Authentication confirms identity, while authorization defines access rights.
3. Why are there two spellings: authorization and authorisation?
“Authorization” is American English, while “authorisation” is British English. Both mean the same thing.
4. Where is authorization or authorisation used?
It is used in software systems, cybersecurity, banking apps, websites, and legal frameworks.
5. What happens if authorization is missing?
Without it, users could access restricted data or perform unauthorized actions, leading to security risks.
Conclusion
Understanding authorization or authorisation is essential in today’s digital world. It’s the invisible system that decides what users can and cannot do after logging in. While the spelling may change depending on region, the concept remains a core part of cybersecurity, software systems, and access management.
Whether you’re building applications, managing data, or simply using online services, knowing how authorization works helps you better understand how your information is protected.